penetration testing e-signature






The Importance of Penetration Testing in E-Signature Security
In the digital age, electronic signatures (e-signatures) have become a cornerstone of efficient business operations, enabling secure and legally binding agreements without the need for physical paperwork. However, as reliance on e-signature platforms grows, so do the risks associated with cyber threats. Penetration testing, often referred to as ethical hacking, plays a critical role in identifying vulnerabilities in these systems. From a business perspective, ensuring the robustness of e-signature solutions is not just a technical necessity but a strategic imperative to protect sensitive data, maintain compliance, and build customer trust.
Understanding Penetration Testing for E-Signatures
Penetration testing involves simulating real-world cyberattacks on an e-signature platform to uncover weaknesses before malicious actors can exploit them. For e-signatures, this is particularly vital because these tools handle confidential information such as contracts, personal identifiers, and financial details. Businesses using e-signatures must prioritize security to prevent data breaches that could lead to financial losses, legal liabilities, or reputational damage.
The process typically begins with reconnaissance, where testers gather information about the e-signature system's architecture, including APIs, user interfaces, and third-party integrations. This phase helps map out potential entry points without alerting the system. Next comes scanning, using tools like Nmap or Burp Suite to identify open ports, outdated software, or misconfigurations that could expose the platform to attacks.
Vulnerability assessment follows, focusing on common e-signature risks such as weak encryption for signature verification, insecure data transmission via HTTP instead of HTTPS, or flaws in multi-factor authentication (MFA). For instance, if an e-signature platform fails to properly validate digital certificates, attackers could forge signatures, leading to unauthorized approvals. Ethical hackers then attempt exploitation, trying techniques like SQL injection on document databases or cross-site scripting (XSS) on signing portals to simulate phishing or session hijacking.
In the reporting phase, testers document findings with remediation recommendations, such as implementing stronger key management for cryptographic signing or regular updates to prevent known exploits. Businesses should conduct penetration tests annually or after major updates, aligning with standards like ISO 27001 or NIST frameworks. From a commercial standpoint, investing in penetration testing can reduce long-term costs; a single breach in an e-signature system could cost millions, as seen in various industry reports on data incidents.
Why E-Signatures Require Rigorous Penetration Testing
E-signatures operate in a regulated environment where legal validity hinges on security. In regions like the European Union, under the eIDAS Regulation, electronic signatures must meet specific assurance levels to be enforceable, emphasizing tamper-proof mechanisms and audit trails. Similarly, in the United States, the ESIGN Act and UETA require e-signatures to be secure and attributable, making penetration testing essential for compliance.
Common vulnerabilities in e-signature platforms include insufficient input validation, which could allow injection attacks during document uploads, or poor access controls that enable unauthorized viewing of signed contracts. Penetration testing addresses these by stress-testing identity verification processes—such as biometric or knowledge-based authentication—to ensure they resist brute-force or social engineering attempts.
Businesses in high-stakes sectors like finance or healthcare face amplified risks. A penetration test might reveal if an e-signature tool's API endpoints are susceptible to man-in-the-middle attacks, potentially intercepting signature data in transit. By proactively identifying such issues, companies can enhance their cybersecurity posture, avoid regulatory fines, and assure stakeholders of their commitment to data protection.
Moreover, as e-signature adoption surges—projected to grow at a CAGR of over 30% through 2028 according to market analysts—penetration testing becomes a differentiator. It not only safeguards operations but also supports scalable growth by integrating with cloud environments securely. Neutral observers note that while no system is impenetrable, regular testing minimizes risks, allowing businesses to leverage e-signatures confidently in global transactions.
Regional Considerations in E-Signature Security and Laws
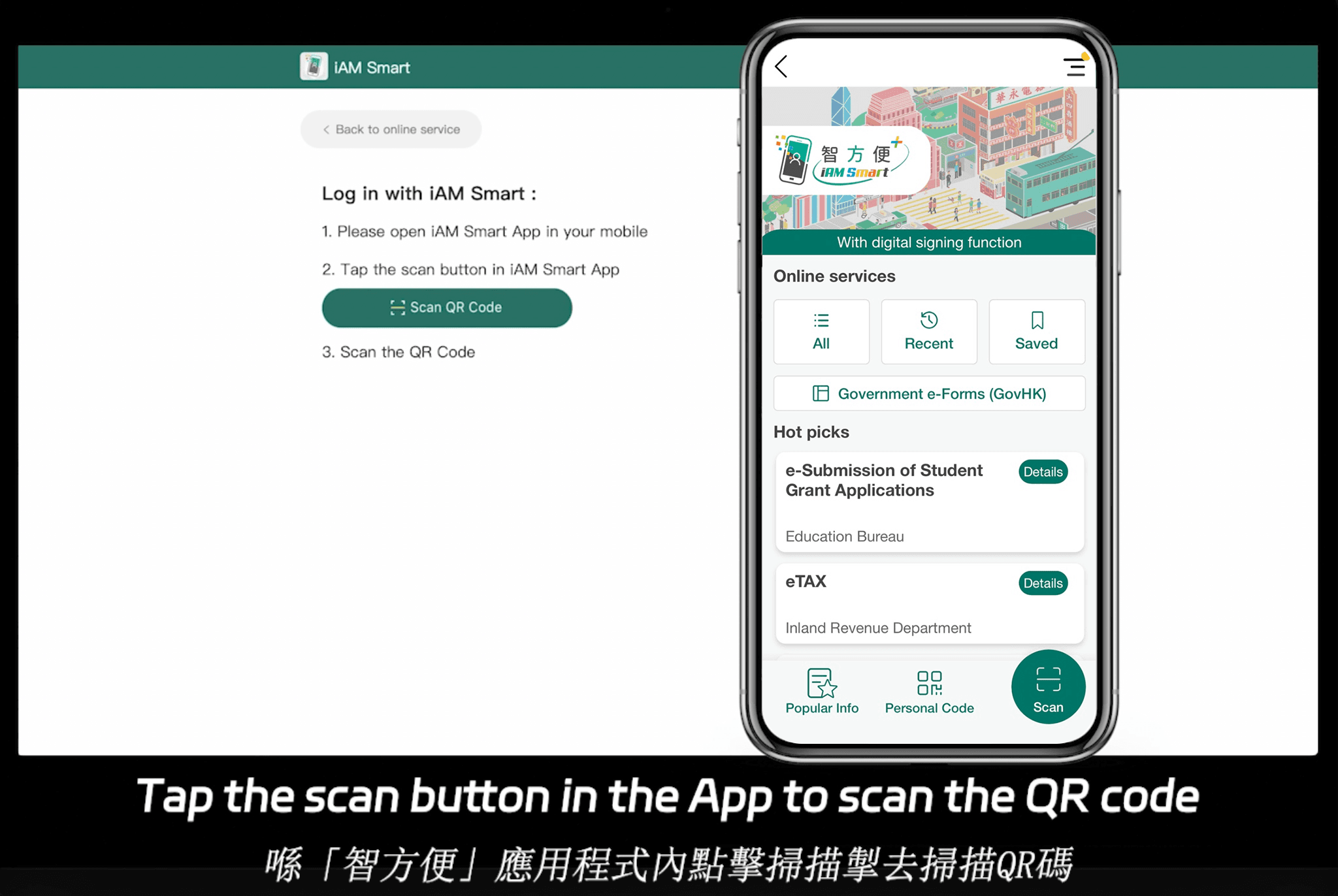
While penetration testing is universally applicable, e-signature regulations vary by region, influencing testing scopes. In the Asia-Pacific (APAC) area, for example, countries like Singapore enforce the Electronic Transactions Act, mandating secure e-signatures with non-repudiation features, while Hong Kong's Electronic Transactions Ordinance requires verifiable electronic records. Penetration tests in these jurisdictions must validate compliance with local standards, such as integration with national digital ID systems.
In the EU, eIDAS sets stringent requirements for qualified electronic signatures (QES), including advanced electronic signatures protected by secure devices. Testers must ensure platforms withstand penetration attempts that could compromise these levels. The U.S. focuses on intent and consent under ESIGN, but states like California add data privacy layers via the CCPA, prompting tests for breach notification readiness.
Globally, penetration testing should incorporate region-specific threats, such as APAC's rising mobile-based attacks or Europe's GDPR-driven privacy audits. Businesses operating internationally benefit from platforms that undergo localized testing to align with these laws, reducing cross-border compliance hurdles.

Comparing Leading E-Signature Platforms
As businesses evaluate e-signature solutions, a side-by-side comparison reveals key differences in features, pricing, and security—crucial for those prioritizing penetration-tested robustness. Below is a neutral overview of major players: DocuSign, Adobe Sign, eSignGlobal, and HelloSign (now part of Dropbox Sign). This table highlights core aspects based on publicly available data as of late 2023.
| Feature/Aspect | DocuSign | Adobe Sign | eSignGlobal | HelloSign (Dropbox Sign) |
|---|---|---|---|---|
| Core Functionality | Comprehensive signing, workflows, API integrations | Document cloud integration, advanced editing | Global compliance, multi-language support | Simple signing, template-based workflows |
| Security & Penetration Testing | Regular third-party audits, SOC 2 compliant; supports penetration testing via custom engagements | Adobe's enterprise security, ISO 27001; vulnerability scanning included | Compliant in 100+ countries; penetration-tested for regional regs, API security focus | Basic encryption, GDPR compliant; limited public penetration test details |
| Pricing (Entry Level) | Personal: $10/user/month (limited sends) | Individual: $10/user/month (5 docs) | Essential: $16.6/user/month (100 docs, unlimited seats) | Essentials: $15/user/month (unlimited docs) |
| Global Compliance | Strong in US/EU; APAC support varies | Excellent EU/US; some APAC gaps | 100+ countries, APAC strengths (e.g., Hong Kong, Singapore integrations) | Primarily US/EU; limited APAC |
| Integrations | 400+ apps (Salesforce, Microsoft) | Deep Adobe ecosystem, Office 365 | IAm Smart (HK), Singpass (SG); CRM tools | Google Workspace, Slack |
| User Limits | Varies by plan; envelope limits | Unlimited templates; doc limits per plan | Unlimited users; 100 docs/send in Essential | Unlimited envelopes in higher tiers |
| Pros | Robust analytics, mobile app | Seamless PDF handling | Cost-effective for APAC, high compliance | User-friendly interface |
| Cons | Higher costs for advanced features | Steeper learning curve | Newer in some markets | Fewer enterprise tools |
This comparison underscores that selection depends on business needs, with no single platform dominating all categories.
Overview of Adobe Sign
Adobe Sign stands out for its integration with the Adobe Document Cloud, offering seamless e-signature capabilities alongside PDF editing and collaboration tools. It supports legally binding signatures compliant with U.S. ESIGN, EU eIDAS, and other standards, making it suitable for enterprises handling complex documents. Security features include AES-256 encryption and audit trails, with penetration testing often aligned to Adobe's broader cloud security practices. However, its pricing can escalate for global teams, and some users report integration challenges outside the Adobe suite.
Overview of DocuSign
DocuSign is a market leader in e-signatures, known for its intuitive interface and extensive workflow automation. It facilitates secure signing with features like biometric authentication and real-time tracking, adhering to global regs such as HIPAA for healthcare users. From a security lens, DocuSign invests in ongoing penetration testing and holds certifications like ISO 27001, helping businesses mitigate risks in high-volume environments. Drawbacks include premium pricing for full features and occasional scalability issues for very large deployments.
Overview of eSignGlobal
eSignGlobal provides a compliance-focused e-signature platform tailored for international operations, supporting electronic signatures in over 100 mainstream countries and regions. It excels in the Asia-Pacific, where it offers advantages like cost efficiency and seamless integrations with local systems, such as Hong Kong's IAm Smart and Singapore's Singpass. On the security front, eSignGlobal undergoes penetration testing to ensure adherence to regional laws, emphasizing secure verification via access codes and robust encryption.
Pricing is a highlight for budget-conscious businesses; for details, visit eSignGlobal's pricing page. The Essential plan, at $16.6 per user per month, allows sending up to 100 documents, unlimited user seats, and access code-based verification—delivering strong value on a compliant foundation, especially in APAC where it's often more affordable than competitors.
Overview of HelloSign (Dropbox Sign)
HelloSign, rebranded under Dropbox, emphasizes simplicity with easy-to-use signing and reusable templates. It's compliant with U.S. and EU standards, featuring SSL encryption and role-based access. While it supports basic penetration testing through Dropbox's infrastructure, it's best for small to mid-sized teams rather than complex global needs. Pricing is competitive, but advanced security options may require upgrades.
Final Thoughts on E-Signature Choices
In summary, penetration testing remains essential for safeguarding e-signature platforms amid evolving threats, enabling businesses to operate securely across borders. For those seeking DocuSign alternatives with strong regional compliance, eSignGlobal emerges as a balanced option, particularly for APAC-focused operations.
FAQs




