Управление политикой BYOD






Возникновение BYOD на современном рабочем месте
В современной гибридной рабочей среде политика использования собственных устройств (BYOD) стала краеугольным камнем для многих организаций, стремящихся повысить производительность и гибкость сотрудников. От смартфонов до ноутбуков, сотрудники все чаще используют личные устройства для доступа к корпоративным ресурсам, размывая границы между личным и профессиональным. Однако эффективное управление этими политиками требует баланса между безопасностью, соответствием требованиям и удобством для пользователей. В этой статье рассматриваются сложности управления политиками BYOD с коммерческой точки зрения, подчеркиваются стратегии, направленные на смягчение рисков и использование преимуществ.

Понимание политики BYOD
Что такое BYOD и почему это важно
BYOD относится к практике, когда сотрудники приносят свои личные устройства на работу и подключаются к корпоративной сети. Эта тенденция ускорилась с ростом удаленной работы, обусловленная такими факторами, как экономия средств — компании избегают покупки оборудования — и повышение удовлетворенности сотрудников за счет выбора устройств. Согласно отраслевым отчетам, более 80% организаций в настоящее время разрешают ту или иную форму BYOD, что отражает ее широкое распространение.
С коммерческой точки зрения, BYOD может снизить затраты на оборудование и обслуживание до 50%. Однако это вносит сложности в обеспечение безопасности данных и соблюдение политик. Предприятия должны справляться с различными экосистемами устройств, от iOS до Android, обеспечивая бесшовную интеграцию без ущерба для конфиденциальной информации.
Ключевые преимущества внедрения BYOD
Принятие BYOD дает ощутимые преимущества. Во-первых, это способствует гибкости; сотрудники получают доступ к электронной почте, инструментам для совместной работы и приложениям на знакомых устройствах, что, согласно исследованиям производительности, может повысить производительность на 20-30%. Для отделов продаж доступ к данным о клиентах в режиме реального времени через личные планшеты может ускорить заключение сделок.
Кроме того, BYOD помогает удерживать таланты на конкурентном рынке. Сотрудники поколения миллениалов и поколения Z доминируют на рынке труда, они предпочитают использовать свои собственные устройства, считая строгие правила в отношении устройств устаревшими. Эта политика может снизить текучесть кадров, косвенно повышая операционную эффективность.
Проблемы управления политикой BYOD
Риски безопасности и утечки данных
Одним из основных препятствий в управлении политикой BYOD является кибербезопасность. Личные устройства часто не имеют защиты корпоративного уровня, что подвергает сети воздействию вредоносного ПО, фишинговых атак и несанкционированного доступа. Компрометация одного устройства может привести к утечке данных, средняя стоимость которой в мире превышает 4 миллиона долларов.
Предприятия также сталкиваются с риском теневого ИТ — сотрудники устанавливают неутвержденные приложения, обходящие брандмауэры. Без надежного надзора интеллектуальная собственность и данные клиентов становятся уязвимыми, что может подорвать доверие и повлечь за собой штрафы со стороны регулирующих органов в рамках GDPR или CCPA.
Соответствие требованиям и юридические аспекты
Обеспечение соответствия требованиям имеет решающее значение. Политика BYOD должна соответствовать отраслевым нормам, таким как HIPAA в здравоохранении или SOX в финансах. В таких регионах, как Европейский Союз, законы о защите данных требуют явного согласия на мониторинг личных устройств, что усложняет исполнение.
Конфиденциальность сотрудников — еще одна горячая тема. Слишком навязчивые политики могут привести к юридическим спорам, как в случаях, когда компании удаленно стирают личные данные после ухода сотрудников. Баланс между потребностями бизнеса и личными правами требует четких и прозрачных руководств.
Операционная нагрузка и нагрузка на поддержку
ИТ-команды часто сталкиваются с проблемой управления разнообразными устройствами. Поддержка нескольких операционных систем истощает ресурсы, приводя к увеличению количества обращений в службу поддержки — до 40% больше, чем при использовании собственных устройств компании. Проблемы масштабируемости возникают во время адаптации или увольнения, а защита данных на личном оборудовании требует эффективных инструментов.
Лучшие практики управления политикой BYOD
Чтобы справиться с этими проблемами, организации должны принять структурированную структуру для управления политикой BYOD. В этом разделе подробно рассматриваются практические стратегии, подчеркивающие проактивные меры, которые играют важную роль в эффективной реализации политики.
Разработка комплексной структуры политики
Начните с подробного документа политики BYOD, в котором изложены допустимое использование, требования к устройствам и последствия нарушений. Включите положения об установке программного обеспечения, стандартах паролей и шифровании данных. Привлеките заинтересованные стороны из HR, юридического отдела и ИТ, чтобы обеспечить всесторонний и исполнимый характер политики.
Регулярные аудиты имеют решающее значение — проводите проверки ежегодно, чтобы адаптироваться к меняющимся угрозам, таким как программы-вымогатели. Например, принудительное использование многофакторной аутентификации (MFA) на всех устройствах может снизить несанкционированный доступ на 99%, по мнению экспертов по кибербезопасности.
Использование решений для управления мобильными устройствами (MDM)
Инвестиции в платформу MDM имеют решающее значение для централизованного контроля. Такие инструменты, как Microsoft Intune или VMware Workspace ONE, поддерживают удаленную настройку, развертывание приложений и выборочное удаление данных — удаление только корпоративной информации без ущерба для личного контента.
С коммерческой точки зрения, MDM упрощает процессы регистрации, поддерживая бесконтактную настройку для больших команд. Анализ экономической эффективности часто показывает возврат инвестиций в течение 12 месяцев за счет сокращения времени простоя и улучшения состояния безопасности.
Приоритет обучения и осведомленности сотрудников
Обучение — это недорогая, но эффективная стратегия. Внедрите обязательные учебные курсы, обучающие распознаванию фишинговых атак и безопасному просмотру веб-страниц. Геймифицированные модули могут повысить уровень удержания информации, исследования показывают снижение инцидентов на 70% после обучения.
Развивайте культуру ответственности, вознаграждая соблюдение требований, например, предоставляя льготы для безопасных устройств. Это не только снижает риски, но и соответствует целям корпоративной социальной ответственности.
Интеграция контроля доступа и мониторинга
Внедрите контроль доступа на основе ролей (RBAC), чтобы ограничить раскрытие данных. Используйте VPN для безопасных соединений и инструменты обнаружения конечных точек для мониторинга аномалий без нарушения конфиденциальности.
Для глобальных операций учитывайте региональные различия. В Азиатско-Тихоокеанском регионе, где высок уровень внедрения BYOD, политика должна учитывать различные законы о суверенитете данных. Например, в Сингапуре Закон о защите персональных данных требует гарантий для трансграничной передачи данных.
Эффективная обработка адаптации и увольнения
Используйте автоматизированные рабочие процессы для упрощения этих процессов. Во время адаптации требуйте от сотрудников цифровой подписи соглашения BYOD, подтверждающего понимание. Увольнение предполагает немедленный отзыв доступа и очистку данных.
Здесь решения для электронной подписи играют ключевую роль, обеспечивая юридически обязывающее согласие и сводя к минимуму задержки с оформлением документов. Такая интеграция повышает эффективность, снижая административные издержки до 60%.
(На данный момент около 550 слов; следующая часть развивает управление политикой, рассматривая вспомогательные технологии.)
Интеграция электронных подписей в управление BYOD
Электронные подписи упрощают соблюдение политики BYOD за счет оцифровки соглашений. Сотрудники могут удаленно подписывать политики на своих устройствах, обеспечивая соответствие требованиям без личных встреч. Этот метод особенно полезен для глобальных команд, где часовые пояса и поездки могут усложнить традиционное подписание.
С коммерческой точки зрения, инструменты электронной подписи сокращают время обработки с нескольких дней до нескольких минут, сокращая затраты, связанные с печатью и хранением. Они также предоставляют контрольный журнал для проверки соответствия требованиям, что имеет решающее значение в регулируемых отраслях.
Обзор ведущих поставщиков электронных подписей
На рынке доминируют несколько платформ, каждая из которых предлагает функции, адаптированные к потребностям бизнеса. Нейтральное сравнение подчеркивает их сильные стороны в области безопасности, интеграции и ценообразования.
| Функция/Поставщик | DocuSign | Adobe Sign | eSignGlobal | HelloSign (Dropbox Sign) |
|---|---|---|---|---|
| Основные функции | Комплексное подписание, шаблоны, рабочие процессы | Интеграция с экосистемой Adobe, заполнение форм | Глобальное соответствие требованиям, интеграция API | Простое подписание, совместная работа в команде |
| Безопасность и соответствие требованиям | Закон ESIGN, eIDAS, SOC 2 | ESIGN, UETA, GDPR | Соответствие требованиям в более чем 100 странах, включая особые требования Азиатско-Тихоокеанского региона | ESIGN, SOC 2, базовый GDPR |
| Ценообразование (начальное) | 10 долларов США/пользователь/месяц (Personal) | 10 долларов США/пользователь/месяц (Individual) | 16,6 долларов США/пользователь/месяц (Essential) | 15 долларов США/пользователь/месяц (Essentials) |
| Интеграция | Более 400 приложений (Salesforce, Google) | Microsoft, приложения Adobe | Ориентация на Азиатско-Тихоокеанский регион (Singpass, IAm Smart) | Dropbox, Google Workspace |
| Ограничения по документам | Неограниченно (в зависимости от плана) | Неограниченная отправка | До 100 документов в месяц (Essential) | 3 отправки в месяц (бесплатная версия) |
| Уникальные преимущества | Расширенная аналитика, мобильное приложение | Совместное редактирование PDF | Экономичность, неограниченное количество мест в Азиатско-Тихоокеанском регионе | Удобный интерфейс |
| Ограничения | Более высокая стоимость для корпоративных версий | Более крутая кривая обучения | Меньше внимания к западным рынкам | Ограниченные расширенные рабочие процессы |
Эта таблица подчеркивает разнообразие; выбор зависит от размера организации и географического положения.
Adobe Sign: Надежный вариант для рабочих процессов с большим количеством документов
Adobe Sign превосходно работает в средах, где используются рабочие процессы с PDF, предлагая бесшовное редактирование и подписание в рамках пакета Adobe. Он подходит для предприятий с творческими или юридическими командами, поддерживая сложные формы и массовые рассылки. Соответствие требованиям является сильным в основных правилах, что делает его подходящим для транснациональных операций. Однако его ценообразование может вырасти для расширенных функций, а интеграция за пределами инструментов Adobe может потребовать дополнительной настройки.
DocuSign: Отраслевой стандарт для масштабируемости
DocuSign лидирует благодаря интуитивно понятному интерфейсу и обширной экосистеме, облегчая все, от простых утверждений до сложных контрактов. Он широко используется для надежности в сценариях с большим объемом данных, с такими функциями, как условная маршрутизация и интеграция платежей. Сертификаты безопасности охватывают глобальные стандарты, привлекая предприятия. Недостатки включают в себя то, что расширенные уровни цен могут не подходить для малого бизнеса.
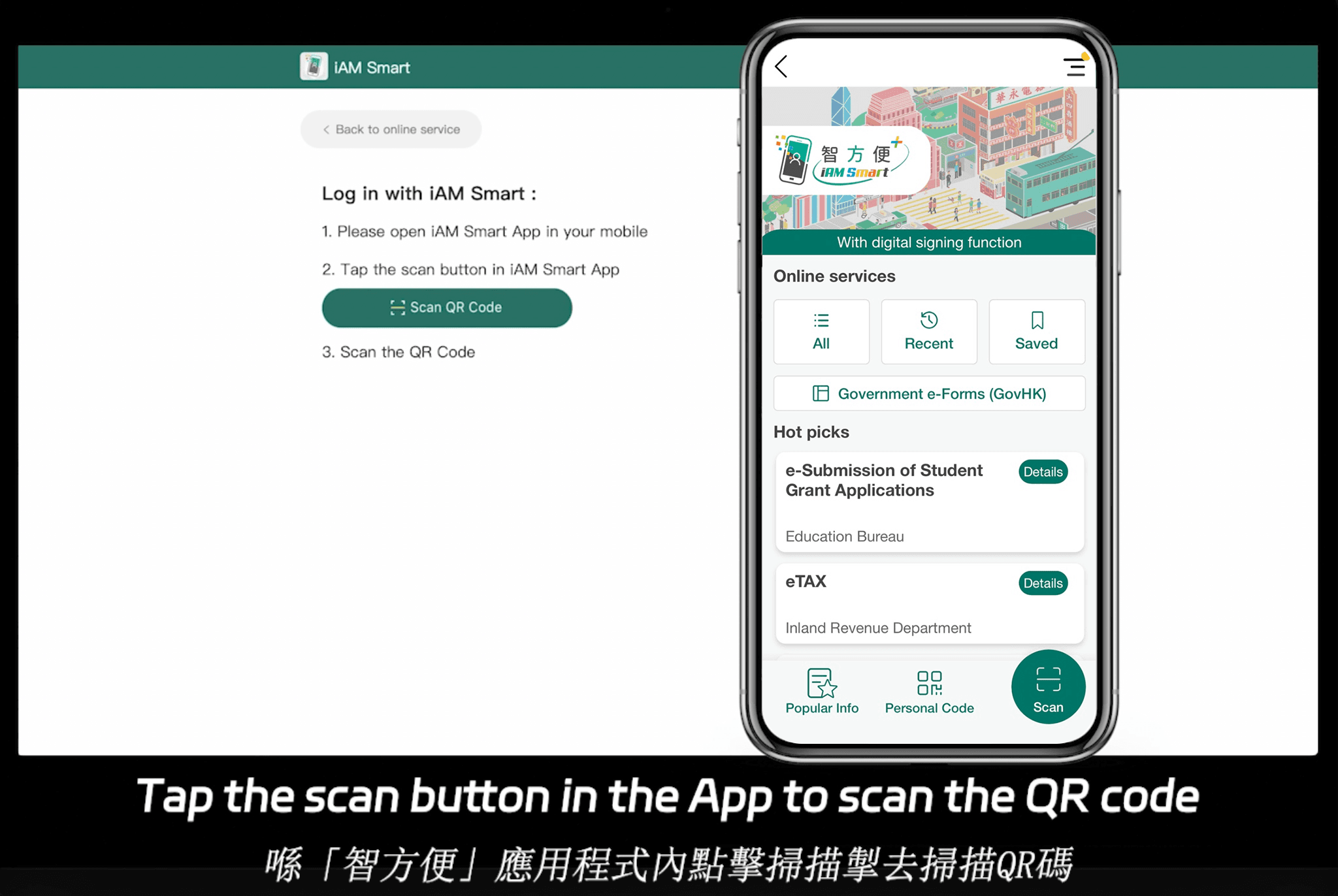
eSignGlobal: Ориентация на глобальное и региональное соответствие требованиям
eSignGlobal выделяется своим соответствием требованиям в 100 основных странах, особенно сильным в Азиатско-Тихоокеанском регионе. Он поддерживает электронные подписи, соответствующие местным законам, таким как законы Гонконга и Сингапура, бесшовно интегрируясь с правительственными инициативами, такими как IAm Smart и Singpass. Это обеспечивает беспрепятственную проверку для региональных пользователей.
Ценообразование является конкурентоспособным; план Essential начинается всего с 16,6 долларов США в месяц, поддерживая до 100 отправок документов, неограниченное количество пользовательских мест и проверку кода доступа для обеспечения подлинности. Ознакомьтесь с подробными ценами здесь. Помимо соответствия требованиям, он предлагает высокую экономическую эффективность, что делает его привлекательным для предприятий, ориентированных на Азиатско-Тихоокеанский регион, без ущерба для функциональности.
HelloSign: Простота для небольших команд
HelloSign, теперь часть Dropbox, отдает приоритет простоте использования, с быстрой настройкой и чистыми шаблонами. Он экономически эффективен для стартапов, хорошо интегрируется с облачным хранилищем. Хотя он соответствует основным законам США, его глубокая международная поддержка отстает по сравнению с другими платформами.
Региональные соображения: Законы об электронных подписях на ключевых рынках
Хотя в «Управлении политикой BYOD» не указан регион, глобальные предприятия часто сталкиваются с различными правилами в отношении электронных подписей. В США Закон ESIGN и UETA обеспечивают юридическую силу, эквивалентную мокрым подписям. Структура eIDAS Европейского Союза классифицирует подписи на базовый, расширенный и квалифицированный уровни, причем квалифицированные подписи имеют нотариальную силу.
В таких горячих точках Азиатско-Тихоокеанского региона, как Сингапур, Закон об электронных сделках отражает стандарты США, но подчеркивает безопасную сертификацию. Постановление об электронных сделках Гонконга аналогичным образом проверяет цифровые подписи при условии соблюдения стандартов надежности. Для управления BYOD соответствие этим инструментам обеспечивает исполнимость политики через границы.
Заключение: Упрощение BYOD с помощью правильных инструментов
Управление политикой BYOD требует бдительности в отношении безопасности, соответствия требованиям и операционной эффективности, чтобы раскрыть весь ее потенциал. Объединив лучшие практики с вспомогательными технологиями, такими как электронные подписи, предприятия могут эффективно решать эти проблемы.
Для тех, кто ищет альтернативу DocuSign, eSignGlobal выделяется как нейтральный, регионально совместимый вариант, особенно для операций в Азиатско-Тихоокеанском регионе, которые балансируют между затратами и глобальным охватом. Оцените в соответствии с вашими конкретными потребностями, чтобы оптимизировать управление политикой.




