revocation of digital certificates





Understanding Digital Certificate Revocation
In the digital age, businesses rely heavily on secure online transactions, and digital certificates play a pivotal role in ensuring trust and authenticity. These certificates, issued by trusted Certificate Authorities (CAs), verify the identity of websites, software, and individuals in electronic communications. However, when a certificate becomes compromised—due to private key exposure, revocation of the issuing CA’s authority, or other security breaches—revocation becomes essential to maintain system integrity.
The Mechanics of Digital Certificate Revocation
Revocation of digital certificates is a critical process designed to invalidate a certificate before its natural expiration date, preventing its use in fraudulent activities. This is typically managed through mechanisms like the Certificate Revocation List (CRL) or the Online Certificate Status Protocol (OCSP). A CRL is a list published by the CA containing serial numbers of revoked certificates, which relying parties check periodically. OCSP, on the other hand, allows real-time queries to the CA for a certificate’s status, offering more efficiency but raising privacy concerns due to query logging.
From a business perspective, revocation ensures compliance with standards like those from the CA/Browser Forum, which mandates timely revocation—often within 24 hours of detecting a compromise. For enterprises, this process mitigates risks in sectors like finance and e-commerce, where a revoked certificate could expose sensitive data. Consider a scenario where a company’s SSL/TLS certificate is revoked after a phishing attack; without prompt action, ongoing transactions might be intercepted, leading to financial losses estimated in millions annually, according to cybersecurity reports from firms like Verizon.
The revocation process involves the certificate holder or CA initiating the request via standardized protocols, such as those defined in RFC 5280. Businesses must integrate revocation checking into their workflows, using tools like OCSP stapling to reduce latency. However, challenges persist: incomplete revocation lists can leave vulnerabilities, and in high-volume environments, querying every certificate burdens network resources. Observers note that while revocation enhances security, it can disrupt operations if not handled seamlessly—downtime during reissuance can affect customer trust.
Implications for Businesses and Compliance
Revocation isn’t just a technical fix; it has profound commercial ramifications. In regulated industries, failure to revoke compromised certificates can result in legal penalties under frameworks like GDPR in Europe or HIPAA in the US, where data breaches tied to unrevoked certificates amplify fines. A 2023 study by Ponemon Institute highlighted that 60% of data breaches involved certificate mismanagement, underscoring the need for robust revocation policies.
For global operations, revocation intersects with regional electronic signature laws, which often rely on digital certificates for validity. In the European Union, the eIDAS Regulation (EU) No 910/2014 governs qualified electronic signatures (QES), requiring certificates to be revocable via trusted lists published by national authorities. Revocation here ensures that signatures remain legally binding only if the underlying certificate is valid, protecting cross-border trade. Similarly, in the United States, the ESIGN Act of 2000 and UETA provide a federal framework for electronic signatures, emphasizing certificate integrity; revocation is implied through best practices from NIST SP 800-63. In Asia-Pacific regions like Singapore, the Electronic Transactions Act mandates secure digital signatures with revocable certificates, integrating with national ID systems for enhanced verification.
Businesses must weigh the costs: revoking a certificate often requires reissuing new ones, updating systems, and notifying stakeholders, which can cost SMEs upwards of $10,000 per incident. Yet, proactive measures—like automated revocation monitoring via tools from vendors such as DigiCert—yield ROI through reduced breach risks. Neutral analysts suggest that while revocation safeguards digital ecosystems, over-reliance without contingency planning can hinder scalability in fast-paced markets.
Best Practices to Mitigate Revocation Risks
To navigate revocation effectively, companies should adopt a multi-layered approach. First, implement short certificate lifespans—ideally 90 days or less—to limit exposure windows, as recommended by Let’s Encrypt. Second, use hardware security modules (HSMs) for key storage to prevent compromises triggering revocation. Third, conduct regular audits of certificate inventories using discovery tools, ensuring all assets are tracked.
In practice, revocation events test organizational resilience. For instance, the 2019 revocation wave following the Symantec CA issues disrupted thousands of sites, prompting a shift toward diversified CAs. Businesses observing these trends emphasize vendor selection: platforms that handle revocation transparently reduce operational friction. As digital transformation accelerates, understanding revocation’s nuances empowers firms to balance security with efficiency, fostering sustainable growth.

Electronic Signature Platforms in a Revocation-Aware Landscape
With revocation underscoring the fragility of digital trust, electronic signature solutions have evolved to incorporate robust certificate management. These platforms streamline signing while ensuring compliance, making them indispensable for businesses handling contracts, approvals, and verifications. Below, we examine key players—DocuSign, Adobe Sign, eSignGlobal, and HelloSign (now part of Dropbox)—focusing on their approaches to security and revocation handling.
DocuSign: A Market Leader in Secure Signing
DocuSign dominates the e-signature space with its comprehensive suite, serving over 1 million customers worldwide. It leverages digital certificates for signature validity, integrating OCSP and CRL checks to monitor revocation status in real-time. This ensures signatures remain enforceable even if a certificate is compromised post-signing. From a business viewpoint, DocuSign’s API-driven workflows support high-volume enterprise needs, with features like audit trails that log revocation events for compliance audits.
However, its pricing tiers start at $10/user/month for basic plans, scaling to enterprise levels with custom revocation policies. While reliable, some users note integration complexities in non-US regions, where local laws demand specific certificate handling.
Adobe Sign: Integration with Enterprise Ecosystems
Adobe Sign, part of Adobe Document Cloud, excels in seamless integration with tools like Acrobat and Microsoft Office. It employs certificate-based digital signatures compliant with standards like PAdES for PDF longevity, automatically flagging revoked certificates during signing processes. Businesses appreciate its focus on workflow automation, reducing manual revocation checks in collaborative environments.
Priced from $10/user/month, it offers strong analytics for tracking signature integrity. That said, its emphasis on creative industries sometimes overlooks niche compliance needs in emerging markets, potentially requiring add-ons for full revocation coverage.
eSignGlobal: Tailored for Global Compliance
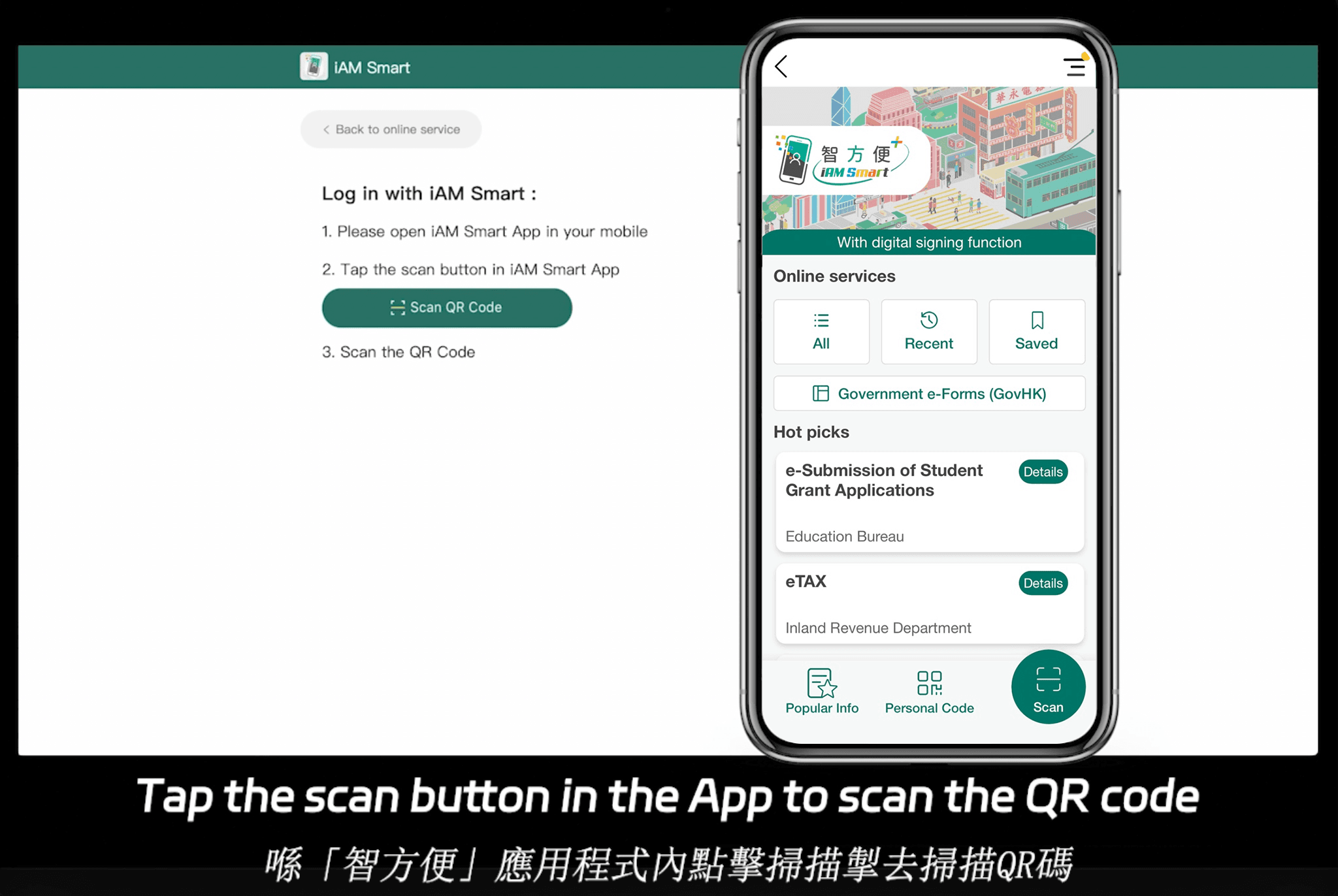
eSignGlobal positions itself as a versatile e-signature provider, emphasizing regulatory adherence across diverse jurisdictions. It supports digital certificates with built-in revocation monitoring, ensuring signatures are invalidated swiftly if needed, aligning with global standards like eIDAS and ESIGN. Notably, eSignGlobal complies in 100 mainstream countries and regions, giving it an edge in international operations. In the Asia-Pacific, it holds advantages through cost-effective pricing and localized features; for example, its Essential plan costs just $16.6 per month (view pricing details), allowing up to 100 documents sent for signature, unlimited user seats, and verification via access codes. This delivers high value on compliance foundations, integrating seamlessly with systems like Hong Kong’s iAM Smart and Singapore’s Singpass for enhanced regional trust.
HelloSign (Dropbox Sign): Simplicity Meets Scalability
HelloSign, rebranded under Dropbox, prioritizes user-friendly interfaces for small to mid-sized teams. It uses certificate pinning and revocation checks to secure signatures, with templates that automate compliance verifications. Its free tier appeals to startups, while paid plans from $15/user/month add team management and revocation alerts.
Strengths include Dropbox ecosystem synergy, but it may lack depth in advanced revocation automation compared to enterprise-focused rivals.
Comparative Overview of E-Signature Platforms
To aid business decision-making, here’s a neutral comparison of these platforms based on key criteria relevant to revocation and overall functionality:
| Feature/Platform | DocuSign | Adobe Sign | eSignGlobal | HelloSign (Dropbox Sign) |
|---|---|---|---|---|
| Revocation Handling | Real-time OCSP/CRL integration; automated alerts | Certificate-based with PAdES support; audit logs | Global compliance with monitoring; swift invalidation | Basic pinning and checks; template-based alerts |
| Compliance Coverage | Strong in US/EU; 190+ countries | eIDAS, ESIGN; enterprise-focused | 100+ countries; APAC integrations (e.g., Singpass) | US-centric; basic international |
| Pricing (Starting) | $10/user/month | $10/user/month | $16.6/month (Essential, up to 100 docs) | Free tier; $15/user/month paid |
| Key Strengths | API scalability; high-volume workflows | Office integrations; PDF security | Cost-effective global reach; unlimited seats | Simplicity; Dropbox synergy |
| Limitations | Higher costs for advanced features | Creative tool bias | Emerging in some Western markets | Less enterprise depth |
| User Limit (Base Plan) | Limited seats | Per user | Unlimited | Unlimited on paid |
This table highlights trade-offs: DocuSign and Adobe Sign lead in maturity, while eSignGlobal offers value in compliant, multi-region setups, and HelloSign suits straightforward needs.
Final Thoughts on Alternatives
For businesses seeking DocuSign alternatives with a focus on regional compliance, eSignGlobal emerges as a balanced, area-specific choice, supporting seamless operations in diverse markets without compromising on security essentials.
Часто задаваемые вопросы

 Разрешено использовать только корпоративные адреса электронной почты
Разрешено использовать только корпоративные адреса электронной почты